What 1,011 Cybersecurity Jobs Actually Ask For
I pulled 1,011 live cybersecurity postings and enriched them with an LLM. CISSP dominates, entry-level is a mirage, remote work is mostly gone, and half of employers still won't post a salary.
Every time someone asks me what they should study, what cert to chase, or whether a given job title is actually entry level, I give the same answer: go read a hundred job descriptions before you spend a dollar. The market is louder than any influencer.
So I did it at scale. On April 6, 2026, I pulled 1,011 live US cybersecurity job postings from public job boards, then ran each one through an enrichment pipeline I wrote that extracts the structured stuff that hiring managers bury in prose: role category, seniority, required and preferred certifications, tools, cloud platforms, languages, salary bands, and remote status. The headline numbers are below. The most useful ones are not the ones I expected.
A short note on methodology
The dataset is 1,011 unique US postings collected April 6, 2026. Seniority, role category, and certification fields are extracted by a combination of keyword rules and a large language model pass over each job description, then reconciled. Salary figures only count postings where a band was explicitly disclosed (490 of 1,011, or 48.5%). Everything below is descriptive: this is a snapshot of what the market said it wanted on one Tuesday in April, not a longitudinal study. The code, the raw CSV, and the chart notebooks all live in a private repo; happy to share with anyone doing similar work.
The CISSP myth
Here is the number that jumped out hardest.
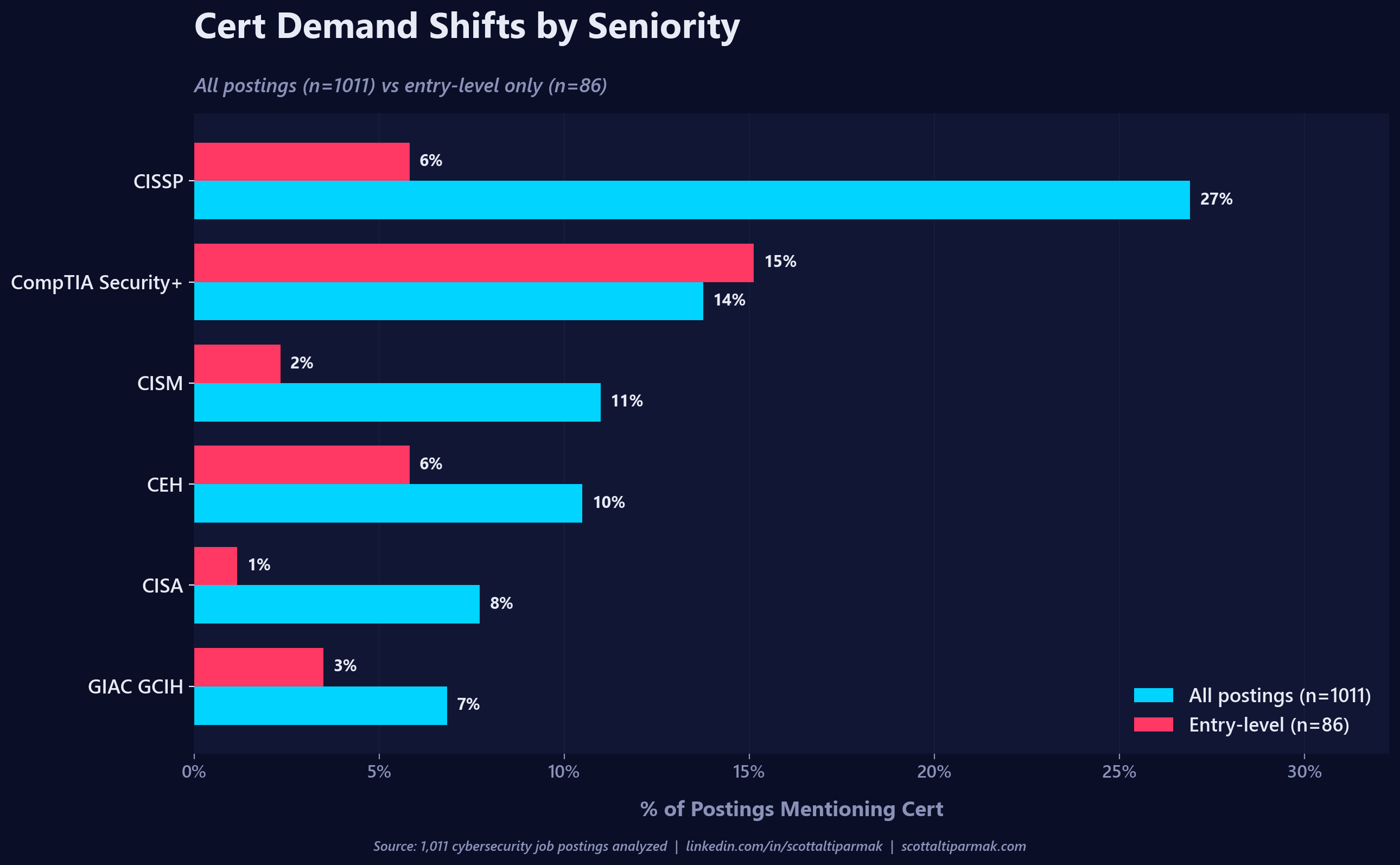
CISSP shows up in 272 of the 1,011 postings. 27%. The single most-requested cert in the entire dataset, by a wide margin.
It also shows up in 5.8% of "entry-level" postings.
That is strange, because CISSP requires five years of paid, full-time security experience across two of its eight domains before a candidate is even allowed to sit for the exam. Candidates can pass the exam as an Associate of ISC2 and bank the credential, but they cannot hold the CISSP itself until the experience requirement is satisfied. Naming it on an entry-level job is, at best, a weak hiring signal.
When I dug into the five entry-level postings where CISSP appeared, none of them actually required it. All five mentioned it in the preferred or "nice to have" bucket. That is a much less scandalous finding than "HR is requiring the impossible," and it is worth being precise about. But the raw data tells a related story that is, in some ways, more useful.
Two of the five postings are literally the same template. A "SOC analyst" posting from a confidential employer and a "Tier 1 SOC Analyst" posting from a staffing firm share the exact same preferred-cert list: CISSP, CEH, GIAC GCIH, GIAC GPEN, GIAC GCIA, GIAC GCFE, CSIS, CSTA, CSTP. Nine certifications, in the same order, on two unrelated companies' postings. That is not two hiring managers expressing their preferences. That is a template someone downloaded, pasted, and forgot to edit. A third posting is a "SOC Analyst II," which is probably my classifier mislabeling a mid role as entry. The remaining two are single appearances of CISSP buried in long "any of these would be great" lists on a McDonald's GRC analyst role and a Clark Creative SOC analyst role.
So the more accurate version of the CISSP myth at entry level is not "impossible requirement." It is "copy-pasted preferred-cert lists on entry-level postings name a credential the candidate cannot legally hold." That is a softer finding, but it is a symptom of something real: the preferred-cert section of a job description is where template rot lives. Nobody reviews it, nobody updates it, and it is the single most reliable place in a JD to spot a posting that was not written by anyone who has hired for the role recently.
Security+ is the actual entry-level standard. It appears in 15.1% of entry postings, 2.6 times as often as CISSP. If you are trying to break in, get Security+. Treat CISSP mentions on entry postings as noise in the preferred section, not as a serious requirement, and definitely not as a reason to spend money on an ISC2 exam you cannot yet hold the credential for.
What the cert market really looks like
Zooming out from the CISSP story, here is the full top ten.
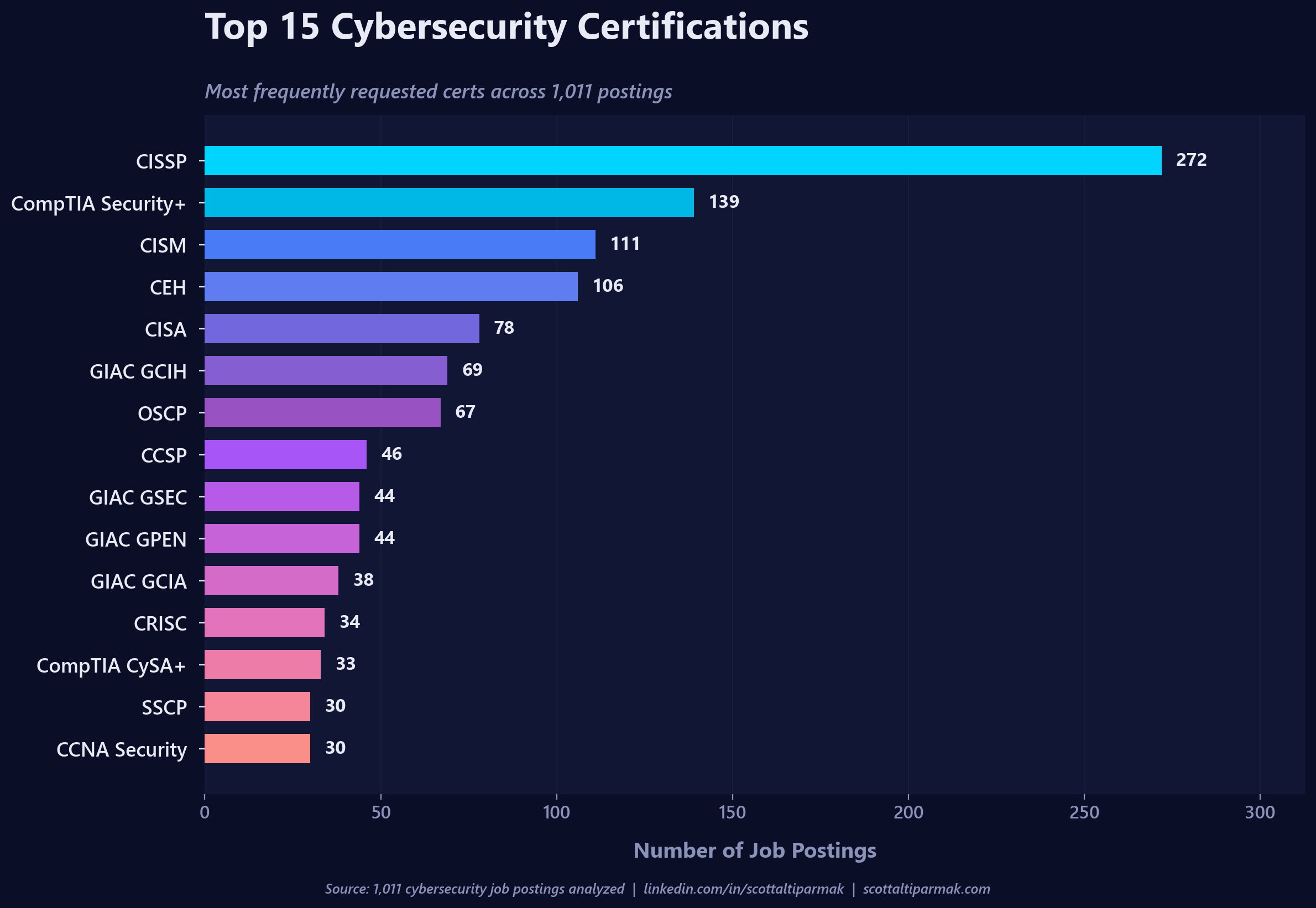
A few things worth naming out loud:
- CEH at 106 postings is still outperforming OSCP at 67. OSCP is the cert practitioners actually respect for offensive work. CEH is the cert HR has heard of. If you are hiring pentesters, the gap between those two numbers is where your hiring bar lives.
- GIAC has three certs in the top ten. GCIH, GSEC, and GPEN. SANS is expensive and the industry complains about the price constantly, but the demand signal is real, especially in incident response.
- CISM at 111 is mostly a management signal. It shows up disproportionately in GRC and Leadership/Management postings, which tracks with how the cert is positioned.
- CCSP at 46 is low relative to how much every company says they care about cloud. Cloud security roles more often want the hyperscaler certs (AWS Security Specialty, AZ-500) than the vendor-neutral CCSP.
The cert market rewards name recognition more than it rewards rigor. That is not news, but it is useful to see in raw counts.
Where "entry level" actually lives
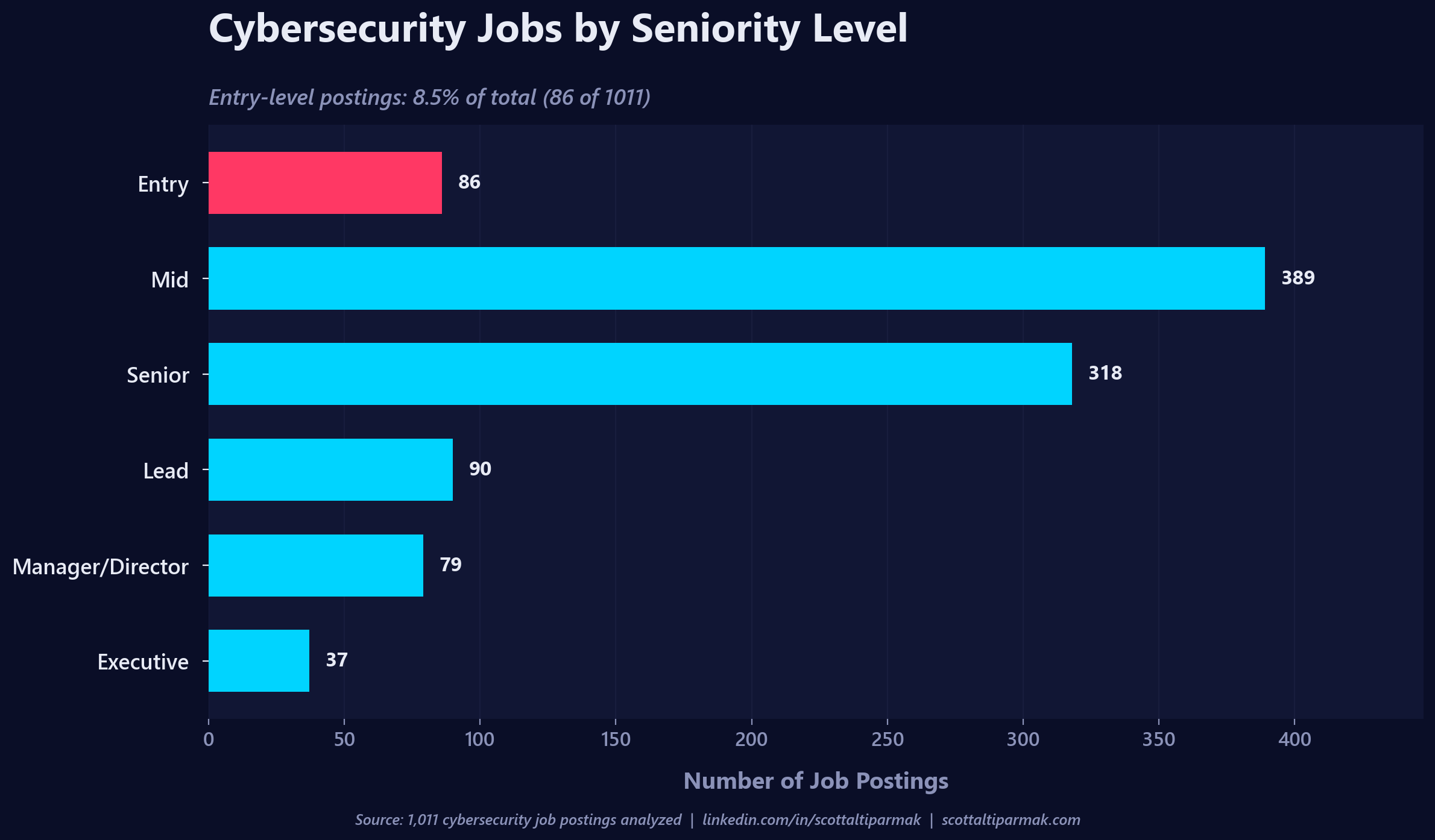
86 of 1,011 postings, or 8.5%, are entry level. That is the real shape of the "cyber talent shortage" conversation that gets recycled every year: the market wants mid and senior people, a lot of them, and it wants them now. Mid and Senior together are 70% of the dataset.
This matches the advice I have been giving students for years and that I wrote up in Breaking Into Cybersecurity: A Roadmap for Students. Cybersecurity is not a first IT job. The market is telling you that loudly. If you are a student or a career-changer looking at that 8.5% number and feeling discouraged, the right move is not to chase the entry-level postings harder. It is to take the helpdesk or sysadmin or network role that gets you adjacent to security, and work the pivot from inside a company that already employs you.
Which kinds of security jobs exist
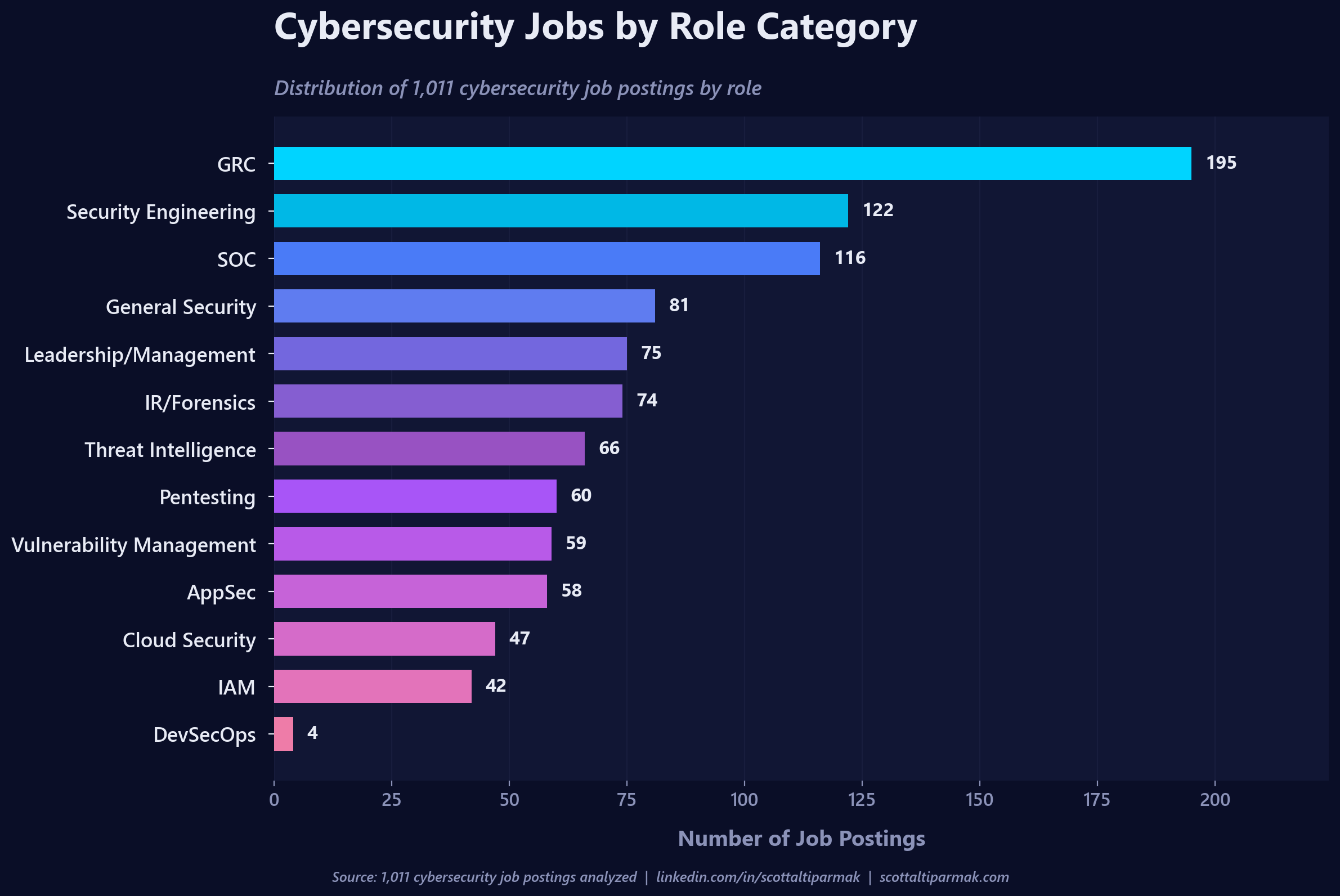
The single largest role category is GRC at 195 postings, almost 20% of the dataset. Governance, risk, and compliance roles do not get the same respect in community conversation as red team or threat intel roles, but the market is spending more on GRC than on any other single category. If your instinct is that security is all hoodies and terminal windows, this chart is a good reality check.
Two numbers I want to flag:
- Pentesting at 60 postings. Six percent of the market. If you are a student building a home lab and grinding OSCP because you want to be a pentester, understand that you are competing for one of the smallest slices of the pie. The career math on pentesting is hard, and it gets harder every year.
- DevSecOps at 4 postings. This one is almost certainly a labeling artifact. The industry keeps saying "shift left" and "DevSecOps" in every keynote, but almost nobody writes a job req with that title. The actual work is buried inside AppSec, Cloud Security, and Security Engineering roles. If you are chasing DevSecOps as a title, you are chasing a hashtag. Chase the skills instead.
Salary, when employers will tell you
Only 490 of the 1,011 postings disclose a salary band. 48.5%. A decade into the pay transparency movement, more than half the market still refuses to commit to a number in the JD.
For the postings that do disclose, the median band is $110,000 to $161,700. Mean is a touch higher at $114,030 to $169,935. That lines up with what you would expect: this is a mid-heavy, senior-heavy dataset, and those numbers are roughly the bands for a mid-to-senior practitioner in a second-tier US metro.
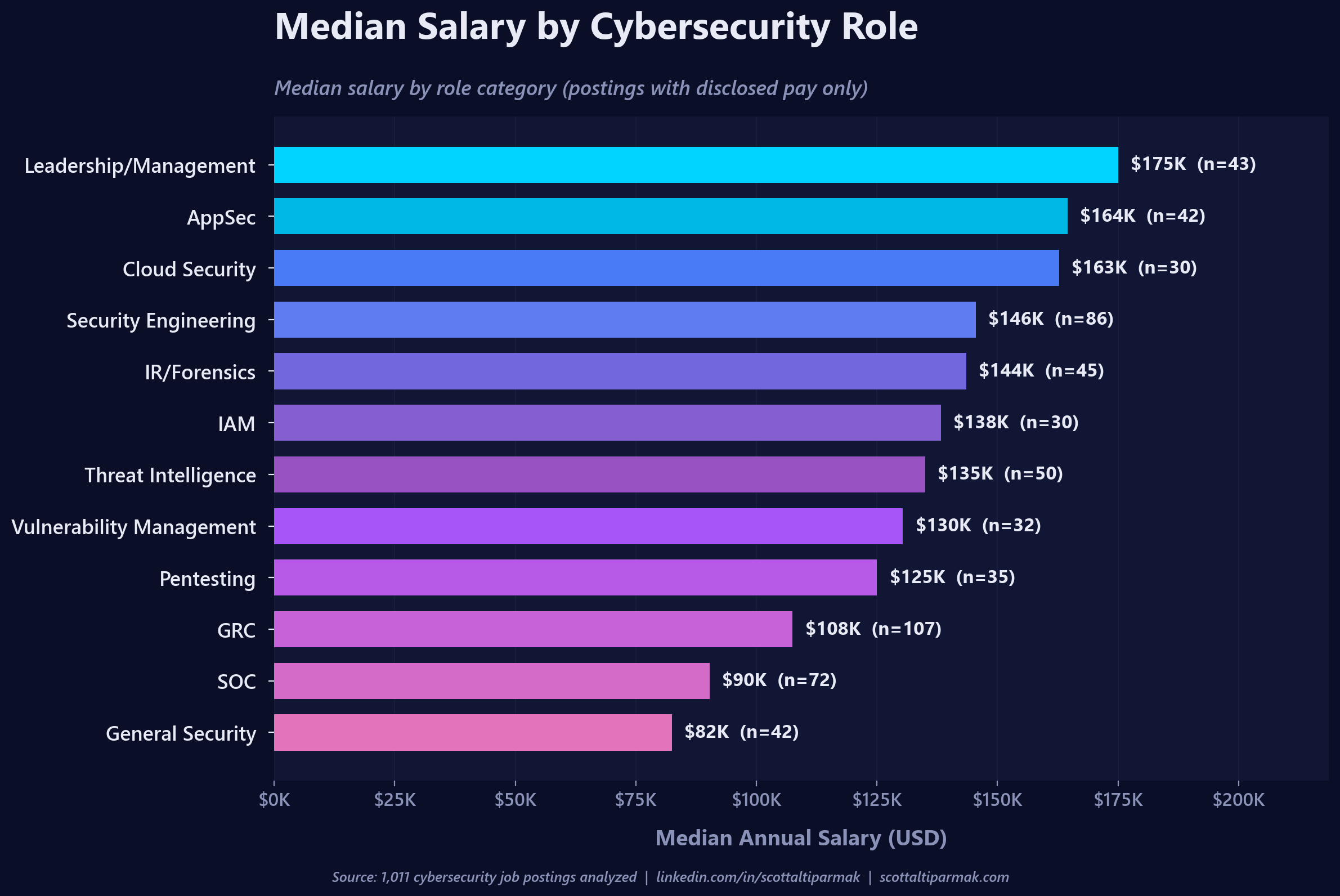
Security Engineering, Cloud Security, and AppSec pay the best. SOC and GRC pay the least. This is not a surprise, but it is a useful correction for students who assume the path into security starts with a SOC analyst role and goes up from there. The SOC floor is lower than most people realize, and the ceiling is lower too. If you want to maximize lifetime earnings, the SOC is a stepping stone, not a destination.
The 51.5% of postings with no salary disclosure are, in my experience, disproportionately the lower-paying ones. Companies that are confident in their bands post them. Companies that are not, do not. Treat a missing band as a signal.
Remote is mostly dead
This one surprised me the most.
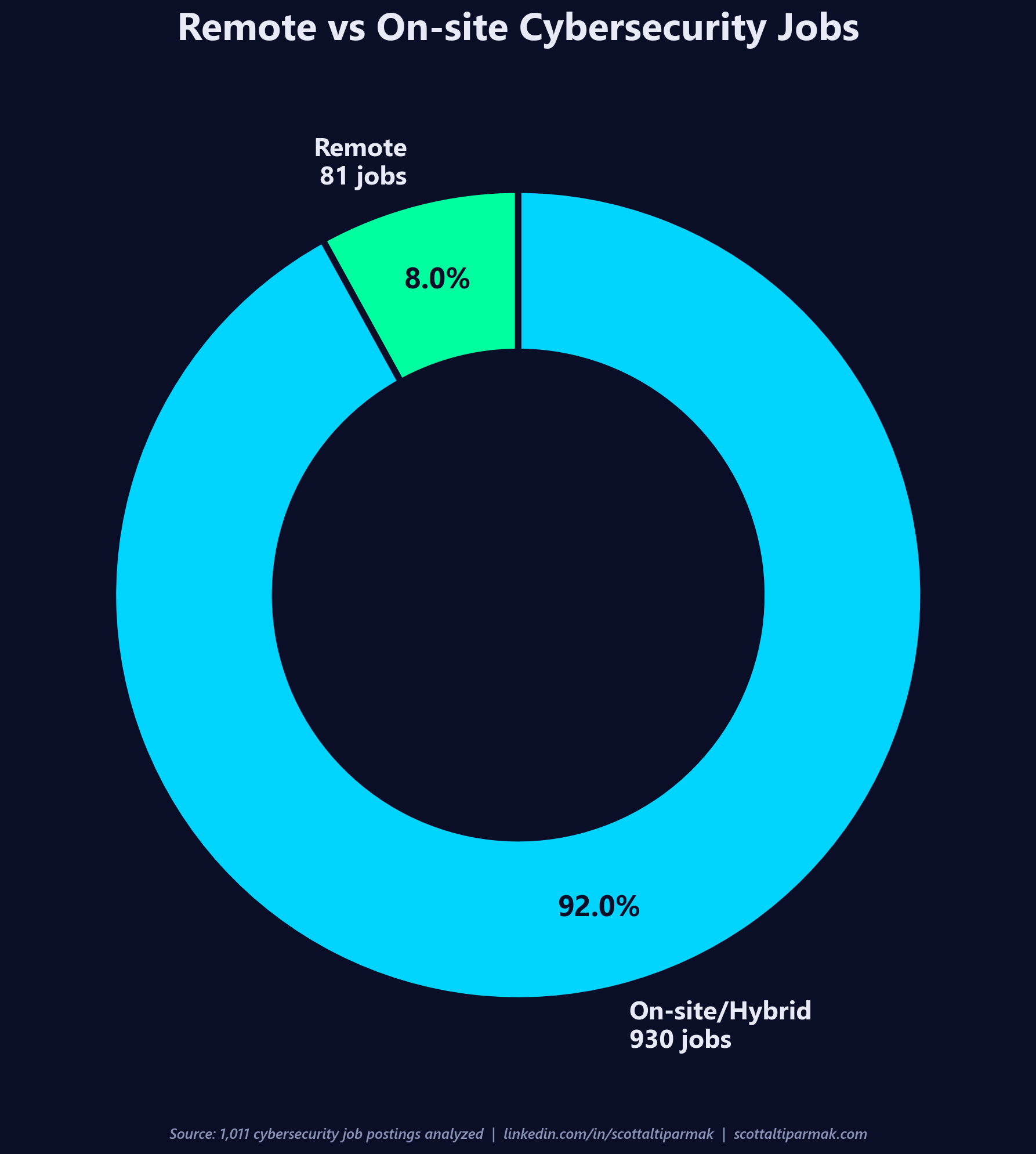
Only 81 of the 1,011 postings are explicitly tagged as remote. 8.0%. The rest are onsite, hybrid, or ambiguously worded in a way that defaults to non-remote. Some of the 92% are certainly hybrid roles with a generous work-from-home allowance, and I did not attempt to separate those from strict onsite requirements in this pass. But the pandemic-era assumption that cybersecurity is a remote-first field is dead in this dataset. If you are optimizing for a remote security career in 2026, you are playing for 8% of the market.
This has knock-on effects for everything else. The remote cybersecurity job is now a scarce asset, which means it is competitive, which means the candidates who land one tend to be senior, well-networked, and already known to the hiring team. Breaking into security remotely from zero is a much harder game than breaking in locally.
What to do with this
If you are a student or career changer:
- Get Security+, not CISSP. Work toward CISSP over years, not months.
- Take the adjacent IT role. The market has 86 entry-level security postings and 389 mid-level ones. You want to be in the mid pool, and you get there fastest from inside a company.
- Look at GRC seriously. It is the biggest slice of the market, it pays adequately, and the work is durable. It is also a great place to build the business context that makes you valuable on the technical side later.
- Do not optimize for remote. The math does not work.
If you are a hiring manager:
- Post your salary band. Half of you are not. The half who are not are getting measurably worse applicants.
- Read your own entry-level JDs. If you require CISSP on an entry posting, you are telling every qualified candidate that your hiring process is broken before they even apply.
- Stop writing "DevSecOps" in your job titles if the actual work is AppSec or Cloud Security. The four postings in the dataset that used the title are a rounding error. The hundreds of postings that describe the work without the title are where the market actually is.
The honest headline of this whole exercise is that the 2026 cybersecurity job market is not the one the industry narrative describes. It is mid-heavy, CISSP-obsessed, onsite, and roughly half-committed to pay transparency. Plan accordingly.
Dataset: 1,011 US cybersecurity postings collected April 6, 2026. Enrichment pipeline written in Python with an LLM extraction pass for structured fields. If you are doing similar work and want to compare notes, reach out on LinkedIn.
More posts
Security Is Applied IT
Most people break into cybersecurity the wrong way. Here is what I actually tell people who ask me how to get started.
Stay in the loop
I write about the security topics that interest me: IAM, cloud security, automation, threat intelligence, phishing, and incident response. If this was useful, there is more where it came from.